I recently had someone ask if there was any way to disable the ability to send a SharePoint news article to an external party and after some clarification it became apparently that even with external sharing completely disabled in the tenant you can, in fact, send a preview of the article to any email address. After some research it became apparent that there is no ability to turn off this functionality which caused some concern of potential data leakage. For reference we are talking about the SharePoint news article 'Send to' functionality shown below.
While a credential is needed to access the full article, any email sent will include an article preview. The article preview doesn't show anything too worrisome as it is just the title, the first few lines of text, and an image but one area that caught my eye was the ability to add in the optional message. After some testing it does not appear that there is any length limit to the text that can be put in the summary, it got me thinking what security controls can you put in place to monitor/control these emails in case someone decided to put in confidential text or even worse a base 64 encoded file.
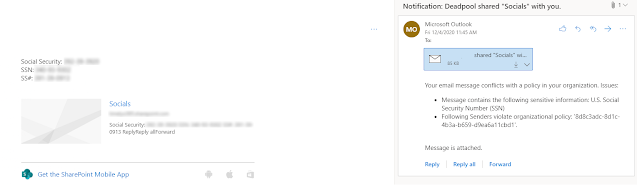
I'll start with the good news. If you are using Exchange Online these emails will respect any DLP policies that you have in place and be routed through the senders email so any email controls that are in place will be respected. In the example below the article named 'Socials' was picked up for a DLP match on a U.S. Social Security Number. This match includes all text in the email including the article title and body as well as any text entered by the user.
Using News Links and News Digest
- Potential for Exploit : Receiving digest emails with malicious links from 'no-reply@sharepointonline.com' can be an area of concern as many organizations may instruct users to trust emails from 'no-reply@sharepointonline.com' due to the usage of SharePoint online.
- Properly configured Safe Links and other email/link scanning can prevent your users from accessing these links in emails.
- Ensure a branding login page is set up for your organization with proper communication and training to prevent credential harvesting. https://docs.microsoft.com/en-us/azure/active-directory/fundamentals/customize-branding
- Medium DLP Risk: News emails sent from a user without Exchange Online are sent from a 'no-reply@sharepointonline.com' email and do not respect any DLP policies
- Low DLP Risk: News emails sent from a user with Exchange Online are routed through the users mailbox and respects any DLP rules that have been set for the organization.







Comments
Post a Comment